Blog
Get the latest updates on our efforts to ensure that the Internet is for everyone.
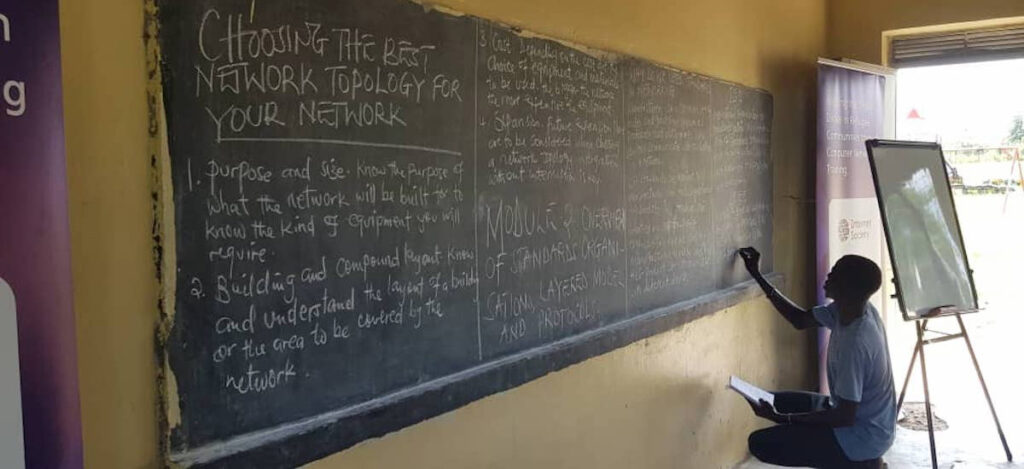
From Email to Case Study: What We Learned About Connecting Refugee Communities in Just One Year
In Uganda’s Rhino Camp Refugee Settlement, we worked with local partners to train refugees and members of the surrounding community …
Local Infrastructure, Lower Costs: How Peering Is Moving the Needle on Internet Affordability
Local infrastructure impacts Internet affordability for users: if the cost is lower and speed and reliability are higher, providers can …
On Global Accessibility Awareness Day, An Internet for Everyone Must Include Everyone
Today, 21 May, marks the 15th Global Accessibility Awareness Day (GAAD)–a day dedicated to getting everyone talking, thinking, and learning about digital …
An Open Fiber Data Standard to Make the Internet for Everyone
The Open Fibre Data Standard is an open data, open standards initiative to develop and implement a common language for …
How RightsCon Is an Unexpected Stress Test for the Multistakeholder Model of Internet Governance
The cancellation of RightsCon 2026 is a stark reminder that when opportunities for civic engagement are neutralized, so are stakeholders’ …
From Coverage to Meaningful Connectivity: How Kenya Is Leading Africa’s Internet Future
In Africa, where the connectivity discussion has traditionally focused on coverage, there’s a recent shift toward making access growth meaningful. Kenya …
Community Snapshot — April
Around the world, our community works locally, regionally, and globally to keep the Internet a force for good: open, globally …
Anatomy of a Scam
Online scams are at an all-time high. But luckily, with the right information and some simple protective habits, you can learn …
Climate and Environmental Sustainability Within the IETF and IRTF
As we celebrate Earth Day 2026, what is the technical community—the people who actually build and operate the Internet—doing about climate and environmental sustainability? …
© Ian Willms / Boreal / Panos