 Researchers at Dell’s Secureworks have uncovered multiple BGP incidents used to steal bitcoins. According to Secureworks, the attacker used a compromised administrator account at a yet undisclosed Canadian ISP.
Researchers at Dell’s Secureworks have uncovered multiple BGP incidents used to steal bitcoins. According to Secureworks, the attacker used a compromised administrator account at a yet undisclosed Canadian ISP.
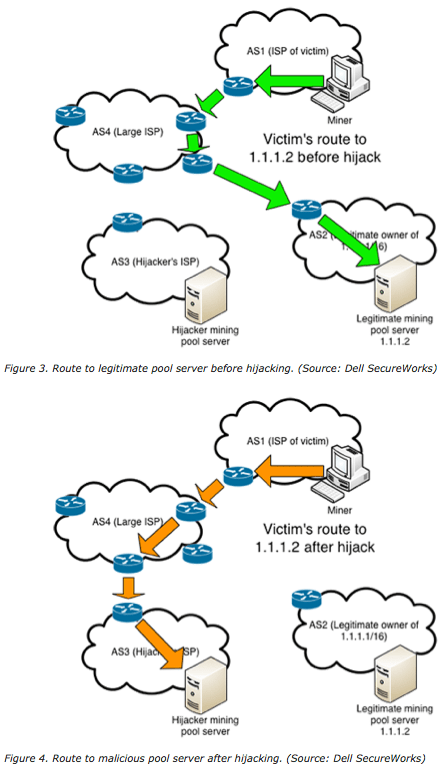
With this account they were able to then inject BGP routes which redirected traffic from machines mining Bitcoins to the attacker’s compromised host. Secureworks estimates that at least $83,000 worth of Bitcoins, Dogecoins, HoboNickels, and Worldcoins were stolen over a period of 4 months.
Details such as the identity of the Canadian ISP or which routes were injected are not included in their report. However, there are two obvious technologies that would have prevented this attack. The first, and most obvious, is Border Gateway Protocol(BGP) security. Something like BGP Resource Public Key Infrastructure (RPKI) would have prevented the receiving BGP peer from accepting bogus routes. The second is Transport Layer Security(TLS) connections between the hosts controlling the *coin miners, and the miners themselves.
If either of these technologies had been deployed in this instance the attack would have been mitigated. The easier of the two is TLS, which only requires the two end-points to start encyrpting their peer-to-peer communications, and does not require anything of the intermediary ISPs. Had the miners been using TLS in this instance, the attacker would not have been able to steal Bitcoins. Instead merely interrupting service for the duration of the hijacking attempt.
The report also contains numerous neat graphics exaplaining how a BGP Man in the Middle(MITM) attack works. They unfortunately use routable IPs in their examples, but the graphics still convey the idea quite nicely.
For more information about TLS, and developing secure applications, check out our page on TLS for Applications. Or visit the IETF’s Using TLS in Applications (UTA) working group.
For more information about Securing BGP, and Secure Inter-Domain routing(SIDR), check out our page on Securing BGP. Or visit the IETF’s Secure Inter-Domain Routing(SIDR) working group.