During the RIPE 66 Anti-Spoofing Panel, a central question where all discussion should start with, is do we have reliable measurements of spoofed traffic? Only with measurements of spoofed traffic size, frequency, and impact, we can conclude if spoofed traffic is a real problem, or just a presumed problem. With the recent Spamhouse DDoS attack, which was a large-scale DNS reflection attack where spoofed traffic is instrumental, we can safely say that spoofing is a problem. Only we see the result, a victim being DDoS’ed, but have to guess where the traffic is originating from. So although we do see the effects of spoofed traffic, it is difficult to quantify the extent of the source of the problem, namely the number of networks that do not properly filter their ingress traffic as suggested by BCP 38. And for the point of discussion, we could argue that the similar egress filtering would even be more effective, but deployment of egress filtering is even more altruistic, where costs and benefit are asymmetric.
Although it is impossible—or practical impossible—to identify the source of spoofed traffic, there are three types of data points that can give us some understanding of the scale and frequency of this phenomena. One data source on deployment of BCP 38 is by means of interviewing network operators on their best practices in managing their networks. One important source of data collected from interviews is Arbor Networks Worldwide Infrastructure Security Report. In two figures, the report summarizes the security measures that are used to protect networks. The network infrastructure security practices figure reports that 57% of the (130) respondents have BCP38/BCP84 anti-spoofing at their network edges. To protect their DNS infrastructure from spoofed traffic, 37% of the respondents installed additional mechanisms (like uRFP). The respondents are a mix of tier 1 and tier 2/3, enterprise and other types of networks. It makes it difficult to put the 57% (or 37% related to DNS infrastructure) figures into context. Anti-spoofing methods at large networks will have a different impact than at the enterprise level. Even though, the results in the Arbor report do give us some impression of the awareness and responsibility operators feel with respect to spoofed traffic.
A more empirical quantitative method to measure the occurrence of spoofed traffic is an indirect method that observes traffic to addresses in a “darknet”. A “darknet” is a range of IP addresses that have never had services running on them. There is no legitimate reason why any traffic is directed to this IP range, but still it happens. At least partly, this traffic is a side-effect of spoofed DDoS attacks (not DNS reflection attacks though) where the attackers hide themselves by spoofing randomly selected source addresses, making it difficult to effectively block it or distinguish between legitimate an malicious traffic. This so-called backscatter traffic measured at “darknets” gives us an idea of the scale of the problem, and by keeping track of this data over time, we can distinguish a trend over the years. The figure below is from the IBM X-Force Trend 2012 Trend and Risk Report and shows the backscatter trend as side effect of spoofed DDoS attacks. This is an interesting plot. Although it gives no absolute numbers in spoofed traffic or networks originating spoofed traffic, it clearly shows an increase in use of spoofed source address in malicious activities. This is consistent with observations by law enforcing agencies (LEAs), which also see an increase in use of spoofed source addresses in (DDoS) attacks.
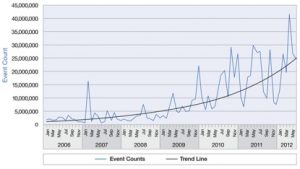
Figure: Backscatter trend as side effect of spoofed DDoS attacks. Data from a “darknet” with aperture of 25,600 addresses. Source: IBM X-Force R&D.
The most consistent and accurate method to measure the potential scale of spoofed traffic would be a direct measurement from all networks globally. The Spoofer project is an example of such an approach, see their contribution to the virtual panel and visit their website http://spoofer.cmand.org. With the Spoofer project people are offered to run a special program in their network to test if the network allows spoofing of a source IP address. The results are collected by servers managed by the Spoofer project. Although there are a number of practical problems to obtain a good representative sample of measurements, data from the Spoofer experiments gives us insight in the number of networks, the prefixes, and the associated size of their address space. These direct measurements complemented with statistical methods give us a good picture of how open the door for spoofed traffic.
Concluding, the three types of measurement touch different aspects of the problem, namely awareness, trend in attacks, and potential sources of spoofed traffic. Combining the results of awareness and potential sources of spoofed traffic, there is room for improvement to reduce the impact of spoofed traffic on network infrastructures. Considering the trend in attacks and their impact, aggravated by the low cost to mount an attack and their untracebility, it is high time for a wider community action. Every effort can help.