In breaking news we learned that ‘Yahoo secretly scanned customer emails for U.S. intelligence’.
Frankly, that is not at all surprising to me. It is a testimony that end-to-end encryption is being deployed to such a level that the spy agencies need to go to the email providers in order to get what they need: the intermediaries or the end-stations. In fact, the Reuters article reporting on this says: “As tech companies become better at encrypting data, they are likely to face more such requests from spy agencies.”
Spyware and its risks
In complying with the intelligence service order the management seemed to have gone around Yahoo’s internal security staff and implemented a program that spied on its customers. There are legitimate questions around why Yahoo complied without questioning the order. It is clear that the rise of encryption has created important questions around responsibilities with respect to law enforcement and intelligence services. Since some may argue there is no societal consensus that this sort of spying is a good thing, those questions need to be answered in a public and transparent debate, not through applying pressure to companies behind closed doors.
One of the apparent reasons why Chief Security Officer Stamos left Yahoo is that he could not assume responsibility for the security hole that was created and impacted the users: ‘Due to a programming flaw […] hackers could have accessed the stored emails.’ The lesson to take out of this is that creating secretive backdoors is a recipe for disasters.
I have argued before that technology companies are in the best position to make their security assessments. And introducing this sort of complex programs into one’s infrastructure does not necessarily improve one’s security. While the timing of Yahoo’s ‘state sponsored’ security breach in 2014 is too early to be causally connected with the installation of the spy-programs in 2015, it is obvious that this sort of interception can have data theft as unwanted side effect.
On Email Encryption
Today, email transport encryption is on the rise due to the availability of IETF technologies like DANE combined with the fact that various entities, including governments, are pushing for the rollout of email transport encryption. However, the encryption of email messages themselves – the content – has not seen significant progress.
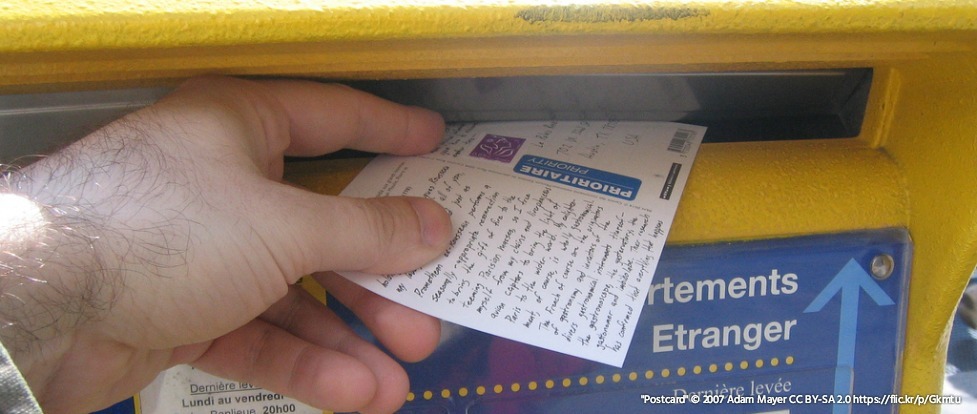
The analogy of the current state of e-mail encryption is that with e-mail we are shipping postcards. While they are in the postal bags being shipped from hub-to-hub, nobody can see what is written on them. But, in the sorting centers and after they’ve dropped on your doormat, everybody can read them. Now, with email being more and more consolidated to big email providers, that doormat is in fact on the webmail-frontend of the Yahoo’s, Google’s, and Microsoft’s of this world. As an aside, the Internet and its services have been designed to be highly distributed. This consolidation, creating obvious control points, is not an inherent part of the Internet’s design and even though the economics are not favorable, I continue to hope that that trend will be reversed sometime.
Back to e-mail confidentiality. It would be better if e-mail encryption would work truly end-to-end, as if we put our postcards in envelopes so that only the recipient can read our correspondence. That is possible. Technologies like S/MIME and PGP are readily available, and have been for decades, but are notoriously hard to use. The fact that many readers may have no idea what those two technology acronyms mean is testimony to the point. The type of usable end-to-end encryption that we see with messaging services is simply not available.
I am a strong proponent of seeing that sort of usable security making it to email and voice communication.
While we do not close our eyes to the impact of the rise of encryption on other societal needs, we at the Internet Society believe that encryption should be the norm for Internet traffic. We actively support projects and technologies that will bring about pervasive encryption as an answer to this kind of pervasive surveillance.
Getting usable email encryption solutions on the users end-devices, so that we can treat your phones, tablets, and computers as metaphorical doormats, is a topic that needs attention from the developers among you. In the meantime, you can only hope that your email provider challenges surveillance orders and enables encryption of the channels between the mail-exchanges (the sorting centers). You can check that yourself through the Internet.nl initiative. If entering your email address shows that a secure connection is not possible, give your provider a call. They are not up to par.
The bottom line is that this latest news about Yahoo should be a rallying cry for end users, developers and, yes, email providers, that usable end-to-end encryption should be available to all. And, as this news demonstrates, time is of the essence.