On July 1st I had few minutes of spare time on my hands, so I decided to go through the procedure of Resource Public Key Infrastructure(RPKI) signing go6lab IPv6 and IPv4 PI resources that I received years ago from RIPE-NCC. I had already setup the validation part on a BGP router previously, learned how that works, and how convenient a system like RPKI helps you with your routing decisions.
However, back then there was no easy way to sign your resources if you had PI address space. After some discussion in the community, RIPE-NCC decided to also deploy the system for PI holders.
With the help of RIPE’s Atlas probes I was able to measure the reachability and visibility of my ASN from many nodes across the global Internet. As you’ll see, nothing broke after I signed the resources. The sky did not fall, my AS remained reachable, nothing unexpected happened, and the entire process took me only 4 minutes 🙂
First about the process, if you are a PI holder in the RIPE region, go to the “RPKI for PI holders” page and read what you need for successful signing of your resources. After you make sure you have everything you need, start the wizard to set up Resource Certifiation for PI End User resources.
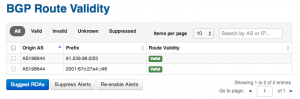
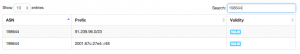
Here you’ll have to enter your ORG identifier, or prefixes that you would like to create ROAs for. Be sure that your maximum lengths match your announced lengths, or you’ll invalidate your prefixes immediately after publishing the ROAs. You can also press “Suggest ROAs” and see if the suggestion is correct, in my case it was. Then you press “Publish ROAs”, and after about 3 hours, needed for ROAs to propagate, you can go to your RPKI validator. Which you installed if you set up RPKI validation for your BGP router. There you can find your resources and also see what the view from the BGP perspective is. They’ll be either Valid, Invalid or Unknown.
After that you can go and check how your BGP routers see your own resources in their Routing Information Base(RIB) if you set up RPKI validation. Hopefully you get the status “valid”.
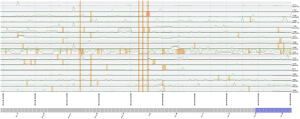
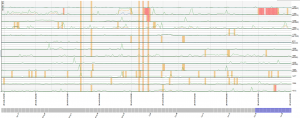
I’m always measuring the global reachability and visibility to the go6lab network. Below you can see, excerpted for clarity and simplicity, that nothing really happened in terms of reachability on July 1st.
Those 3 lines of breakage are because the owner of the building where Go6lab is decided to replace the main power switch with a new one. This caused 3 major outages throughout July 3rd that my UPS’s did not manage to cover 🙁
So, operators and netizens, please go and sign your IP resources and setup the RPKI route validation on your routers. If you follow RIPE’s advice and install invalid routes with localpref 90, and not reject the route, this can become a powerful tool to protect us all from route mis-originations. This tool will only be useful if everyone deploys it and starts using it. So please, go and deploy it 🙂
The next step, and possibly a topic for my next post, would be to invalidate ROAs and measure what happens. How many BGP routers on the Internet are rejecting invalid routes as opposed to installing them with a localpref 90? As suggested on RIPE-NCC RPKI resources set-up site.
For more information on Securing BGP visit our Securing BGP start page.