I just finished reading a recently published “Worldwide Infrastructure Security Report” by Arbor Networks. It is the eighth one in the series of annual reports produced by the company.
Much of the report is based on a survey of 130 respondents from a mixture of Tier 1, Tier 2/3, enterprise, and other types of network operators from all around the world. The survey shows some interesting trends, including the growing threat to and from the mobile world. While the connection speeds are increasing sharply, especially with the advance of the LTE, and new vulnerabilities are discovered on handheld devices, many mobile providers lag behind, continuing to be reactive.
Another visible change is a concern about the “advanced persistent threat” (APT), absent in the previous report. For those not familiar with the term, it represents “well-funded, organized groups of attackers, able to mount sophisticated attacks” as Mandiant describes them. They penetrate the victim’s infrastructure, remain there undetected for a long period of time stealing data, and vanish while leaving the back door open to come back later. They are not “hackers.”
While DDoS attacks continue to represent the most visible threat, their motivation, target, and impact are different from APT. According to the report the top three most commonly perceived motivations for DDoS attacks are political/ideological, online gaming, and vandalism/nihilism infrastructure. In contrast, the main objective of APT is espionage, motivated by political or commercial interests.
More than a quarter of Arbor’s respondents are concerned about APT, but it is not clear what they plan to do about that. With APT, conventional information security defenses don’t work. Detection, mitigation, and even cleanup of such attacks require different methods and strategy. And one should not forget about USB sticks and BYOD. Seems it may require a cultural change towards information security in a company.
There are also some trends measured by the Arbor’s ATLAS system. One of them is ATLAS Average Monitored Attack Sizes Month-By-Month.
The trend is clear and not surprising – a 55% increase over 20 months. This is an unfortunate trend, but let’s not forget that the Internet is growing, too.
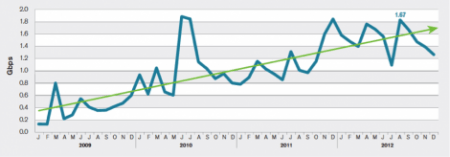
Picture: ATLAS Average Monitored Attack Sizes Month-By-Month (January 2009-Present), source: Arbor Networks, Inc.
Interestingly, over the same period, the average speed of connections, according to Akamai’s State of the Internet Report, increased by 40-50% depending on the region. And the number of broadband subscriptions, according to ITU statistics, has also grown by a moderate 5-8% in Western Europe and North America to over 30% in Russia and China, for example.
Does the Internet outgrow the DDoS threat? I don’t think the numbers give an answer to that question; they are averages and in some way we are comparing apples and oranges. But the growth of the Internet is probably something we need to relate to when we look at the numbers in security reports.
