 Can you please help out with efforts to measure the number of DNSSEC-validating DNS resolvers out there?
Can you please help out with efforts to measure the number of DNSSEC-validating DNS resolvers out there?
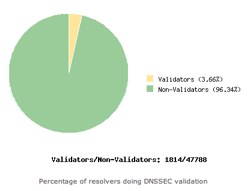
The folks at Verisign Labs are conducting some research into trying to understand what level of DNSSEC-validating resolvers are out on the open Internet. This is critical to understand as the availability of DNSSEC-validating resolvers is a key piece of getting DNSSEC deployed.
They are asking for your help.
If you operate a website, they are asking if you can please add one line of HTML to your site, preferably in a page header, footer, sidebar or other component that gets frequently loaded:
That’s it! As they say on their page:
This HTML snippet should have no visible impact on a rendered page. Since nearly all web browsers now implement DNS prefetching, the code above results in a DNS query for the name shown and allows us to characterize the recursive name server that the query goes through.
They also mention that you can alternatively modify the HEAD element of your page to include this one line of code:
I’ve chosen this latter approach here at Deploy360 and as a result visitors to our site will be helping with this important research. If we can get more sites adding this code, Verisign Labs can get that many more data points feeding in and helping them characterize the level of DNSSEC validating resolvers out there.
Here at Deploy360, we are in favor of research like this because we’d like to get a baseline now and then see trends over time. Encouraging the wider deployment of DNSSEC-validating resolvers by ISPs and other network operators is one of the key activities we are planning to work on over the next 12 months – and this research will help us and many others understand how successful we are collectively in encouraging that deployment.
Can you please help you by adding a line of code to your site? (Thanks!)
P.S. For those curious to learn more about “DNS prefetching” (also called “pre-resolving” by some) and how this research works, here are some articles you may find of interest:
- Chromium Project: DNS Prefetching and related blog post from September 2008
- Mozilla Firefox: Controlling DNS prefetching and an explanation in a blog post
- Microsoft IE: Internet Explorer 9 Network Performance Improvements (“DNS pre-resolution” discussed later in the article)
- Fascinating cautionary tale: “DNS Prefetching Implications” about how the way a site/service was constructed had implications that caused prefetching to incur significant costs for the company.
