Blog
Get the latest updates on our efforts to ensure that the Internet is for everyone.
From Commitments to Practice: Internet Society’s Priorities for WSIS+20 Implementation
Drawing on our strategic priorities, this blog post outlines where we will focus our efforts in supporting the implementation of …
Final Results of the 2026 Internet Society Board of Trustees Elections and IETF Selections
The Internet Society Elections Committee is pleased to announce the final results of the 2026 elections and the IETF selections for the Board …
Community Snapshot—March
Our global chapters work to keep the Internet a force for good. This brief overview covers just some of their …
DNS Blocking: Mind the Unintended Consequences
As DNS blocking mandates multiply, so do concerns about security, the openness of the Internet, and fragmentation …
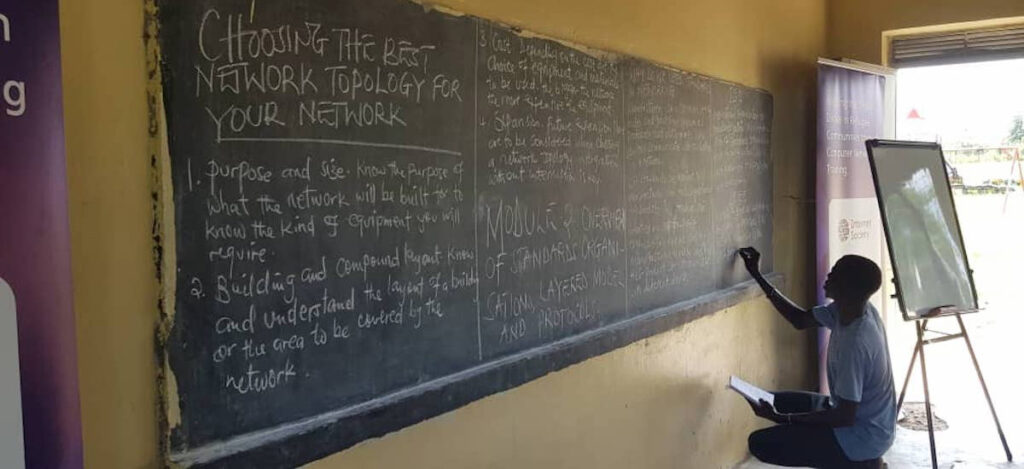
Digital Inclusion and Indigenous Connectivity
The community-centered connectivity model can help advance connectivity efforts in Indigenous communities across the US and beyond …
US Supreme Court Unanimously Defends Internet Access for Millions
The United States Supreme Court’s unanimous decision in Cox v. Sony confirms that ISPs cannot be forced to monitor and …
Keeping the Internet Open for Business
A permanent WTO commitment to not impose customs duties on electronic transmissions would help keep the Internet open and global, …
Connecting Remote Glaciers to Protect Communities in Kyrgyzstan
The Internet Society Kyrgyzstan Chapter is bringing connectivity to remote areas, enabling continuous data collection to keep communities safe …
The NDSS Symposium 2026 Had a New Vibe—But Why?
The NDSS Symposium 2026 hit the sweet spot in terms of substance, energy, and weather. But ultimately, the presenters made …
© Ian Willms / Boreal / Panos