The Internet Society is focused on ensuring that a healthy, sustainable Internet is available to everyone – today and for the next billion users. Technology-focused programs are a vital component of the Internet Society’s mission. We work to facilitate the open development of standards, protocols, and administration, and to ensure a robust, secure technical infrastructure.
Technology
Spectrum: The Natural Resource That Makes Wireless Connectivity Work
Spectrum is one of the most essential—yet least visible—parts of the Internet ecosystem. It’s the foundation that enables billions...
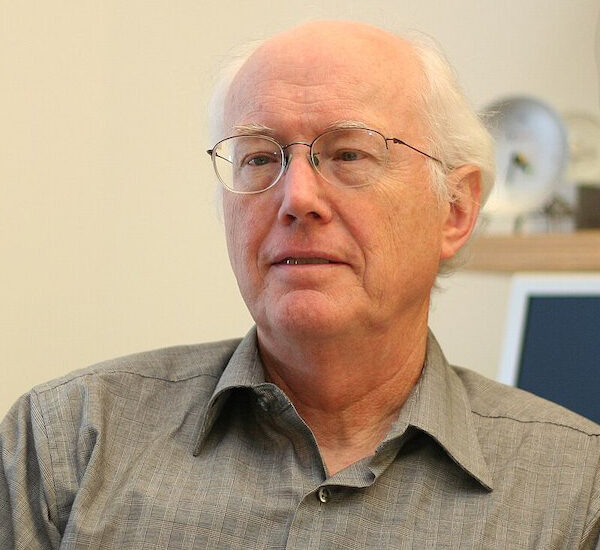
2025 Postel Awardee David Clark, an Architect and Implementer of the Internet
We are proud to announce David Clark as the winner of the 2025 Jonathan B. Postel Service Award! This...

The Internet of Wonder: How a Scientific Livestream Became a Cultural Phenomenon
A scientific expedition in Argentina is becoming a cultural phenomenon thanks to the Internet, pulling in thousands of livestream...
NDSS Symposium 2023
The Network and Distributed System Security (NDSS) Symposium is an annual symposium focused on the latest developments in network...

HOW TO NARROW GAPS IN THE DIGITAL WORLD: BUILD UP TRAINING & BREAK DOWN STEREOTYPES
HOW TO NARROW GAPS IN THE DIGITAL WORLD: BUILD UP TRAINING & BREAK DOWN STEREOTYPES dotmagazine

Common Internet Network Interconnection and Charging Practices
The networks of the Internet charge their customers for access to the Internet regardless of the direction of the...
NDSS Symposium 2022
The Network and Distributed System Security (NDSS) Symposium is an annual symposium focused on the latest developments in network...

How Consumers are Adapting to Voice Technology in the Smart Home
How Consumers are Adapting to Voice Technology in the Smart Home Kardome

The Metaverse Is Simply Big Tech, but Bigger
The Metaverse Is Simply Big Tech, but Bigger WIRED

The Week in Internet News: Facebook Rebrands After Controversies
Facebook Meta-morphosizes; high-speed hacking; Iberian Internet expansion; even more satellite broadband; Internet shutdown in Sudan

The Week in Internet News: Snowden Warns of Anti-Encryption Efforts
Snowden speaks out at Global Encryption Day; Russia censors Internet comms; housing broadband issues; Facebook renaming?; Trump's Truth Social

The Week in Internet News: Using Esports to Fight Cybercrime
International cybersecurity competition; LinkedIn cuts China services; illegal source code; privacy doorbell issues; playing no favorites